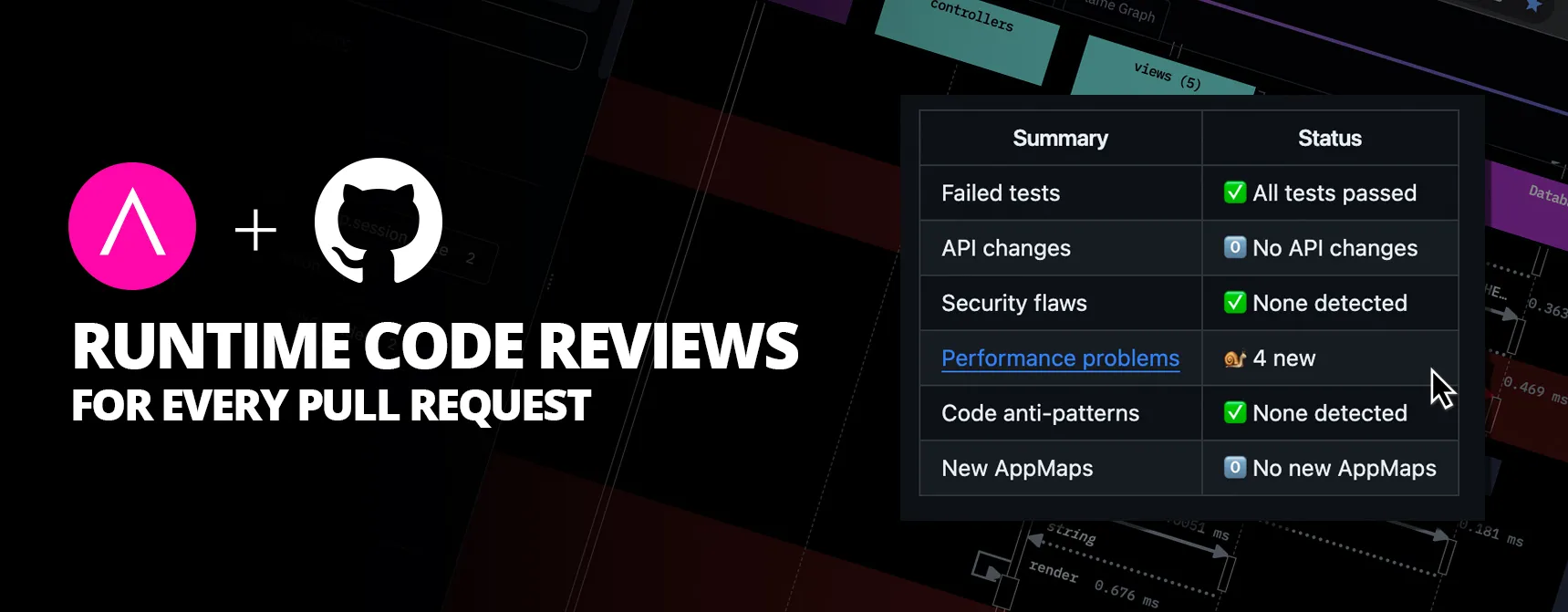
Today, unexpected code behavior and deep runtime defects are responsible for a staggering 40% of performance problems and 50% of security concerns in software development. AppMap addresses this issue head-on, automatically documenting code behavior changes and reviewing code for breaking runtime changes in continuous integration (CI).
AppMap’s new GitHub Action compares runtime code behavior before and after a code change and identifies critical performance, security, and stability issues before merging. These are changes static code analyzers can’t identify.
AppMap’s easy-to-use GitHub Action puts runtime analysis in your existing CI/CD workflow. AppMap’s users say it’s like having a robot architect review every code change.
“Security and performance reviews are part of the process on any engineering team, and ours is no different. It can take months to find issues and weeks to fix problems using static analysis and code reads. With AppMap, that time is reduced to minutes.”
-Padraig Coffey, CEO at Zartis.
AppMap’s analysis goes beyond where static tools can’t with accurate, up-to-date runtime analysis and visualizations of code behavior with direct linkage to the code involved.Paired with AppMap’s integrated code editor experience in VS Code and JetBrains, automated runtime code review is now a seamless part of the developer experience.
“When we initially adopted AppMap, we were only using it for visualizing N+1 queries locally. We later integrated it into our CI run, and we are finding the GitHub comments posted by AppMap to be very useful. The OpenAPI integration, in particular, was a surprise: it’s nice to see an automatically generated summary of what endpoints have changed in a PR.”
-Paul Kuruvilla, CTO at CodeCrafters.
PR comments with runtime review of your code
✅ AppMap issues a summary report of its runtime analysis as a comment on every PR. The example below shows a code change that introduces four new performance flaws that create problems at runtime.
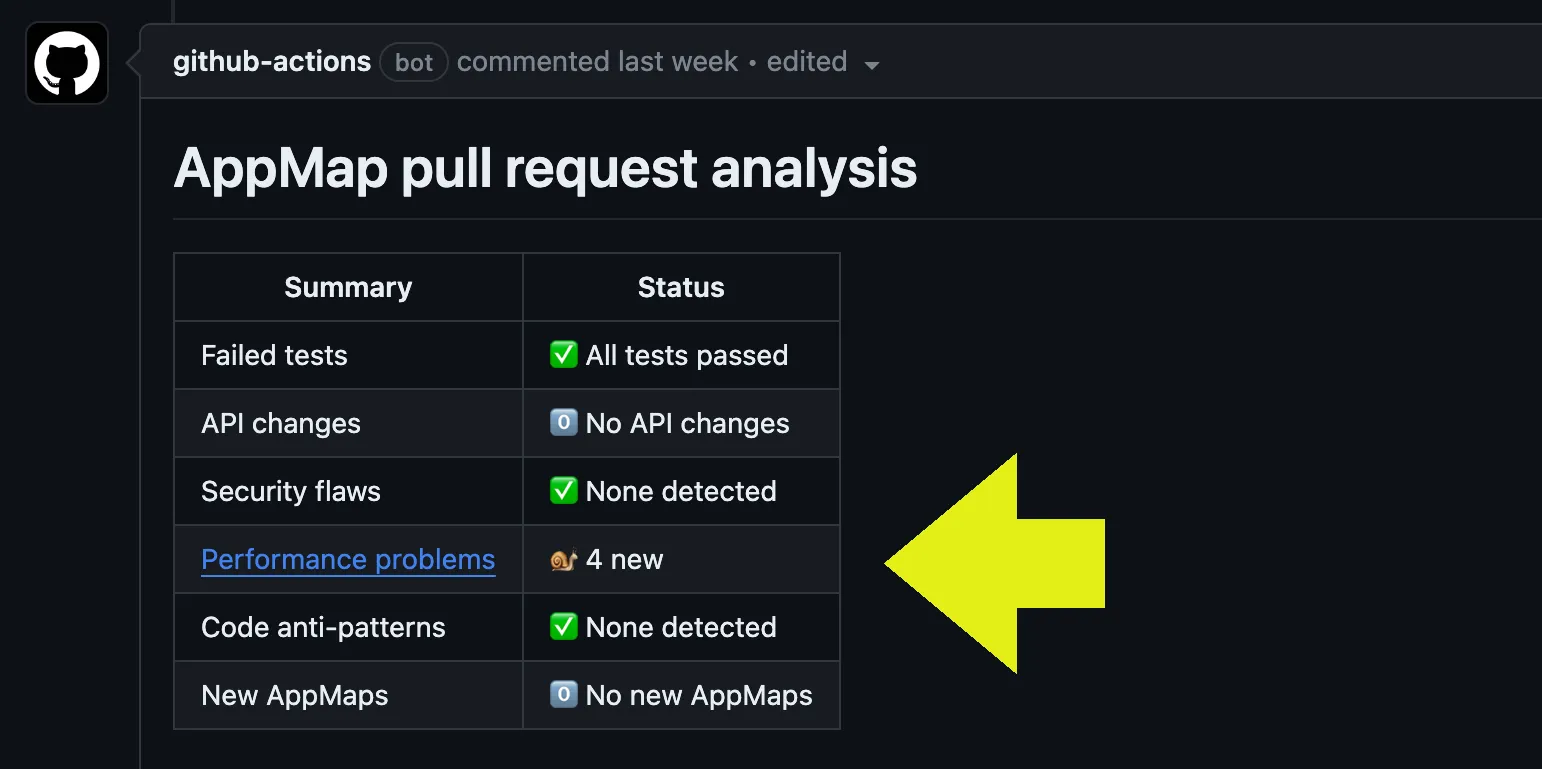
The AppMap pull request report includes details about the flaws detected, a stack trace, and links to the offending source code.
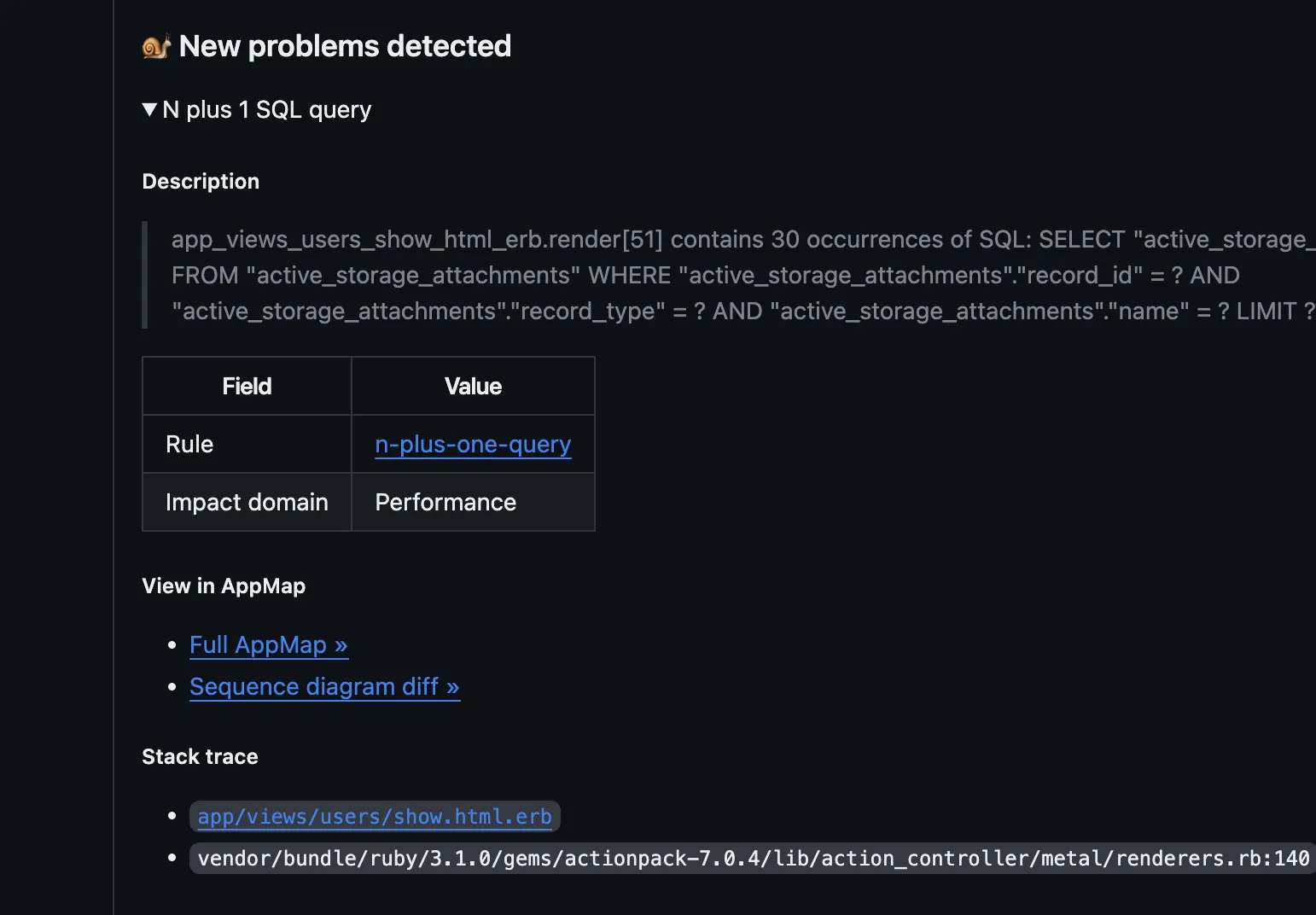
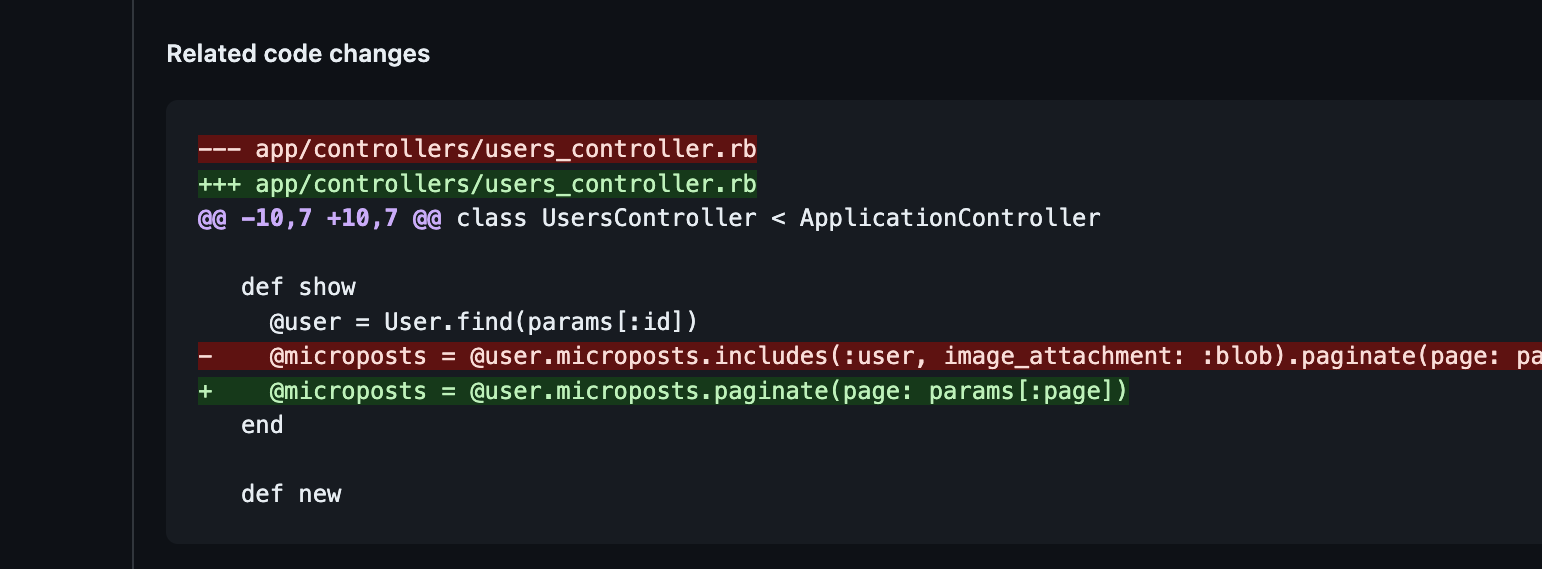
AppMap highlights specific code changes that are contributing to the flaw.
AppMap also links to a full set of interactive visualizations describing the code change and highlighting the flaw. The example below shows a sequence diagram “diff” of the changed runtime behavior.
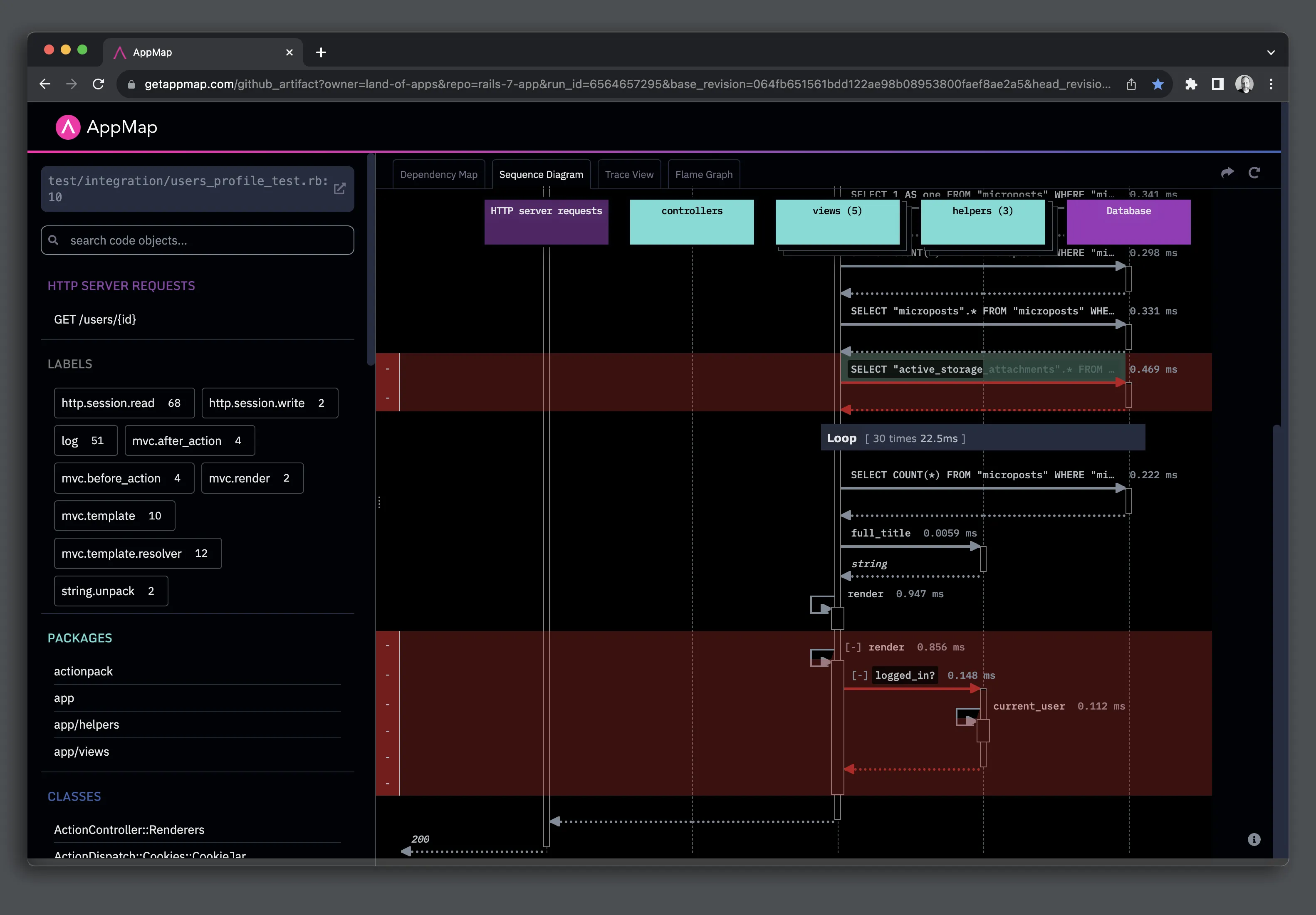
All AppMap Diagrams are stored as artifacts in your GitHub build system and are only rendered using AppMap’s viewer. You don’t have to send your data to a third-party SaaS. Your data stays with you.
AppMap presents information within pull request comments in four key categories:
-
Failed tests
Identify the root cause of test failures with detailed insights and direct links to the line of code which caused the error. AppMap also includes source diffs and behavioral sequence diffs for efficient debugging. -
API Changes
Detect API route differences, including new, deleted, or modified routes, as well as alterations in response attributes like body, content, and descriptions. -
Security flaws only visible at runtime
Uncover issues such as deprecated cryptography algorithms, improper session management, and unauthorized access. -
Performance problems
Identify performance problems like N+1 SQL queries, slow function calls, and sluggish HTTP requests. AppMap ensures your changes are optimized before they reach production.
Here is an example of AppMap describing a security flaw and the code change that produced it.
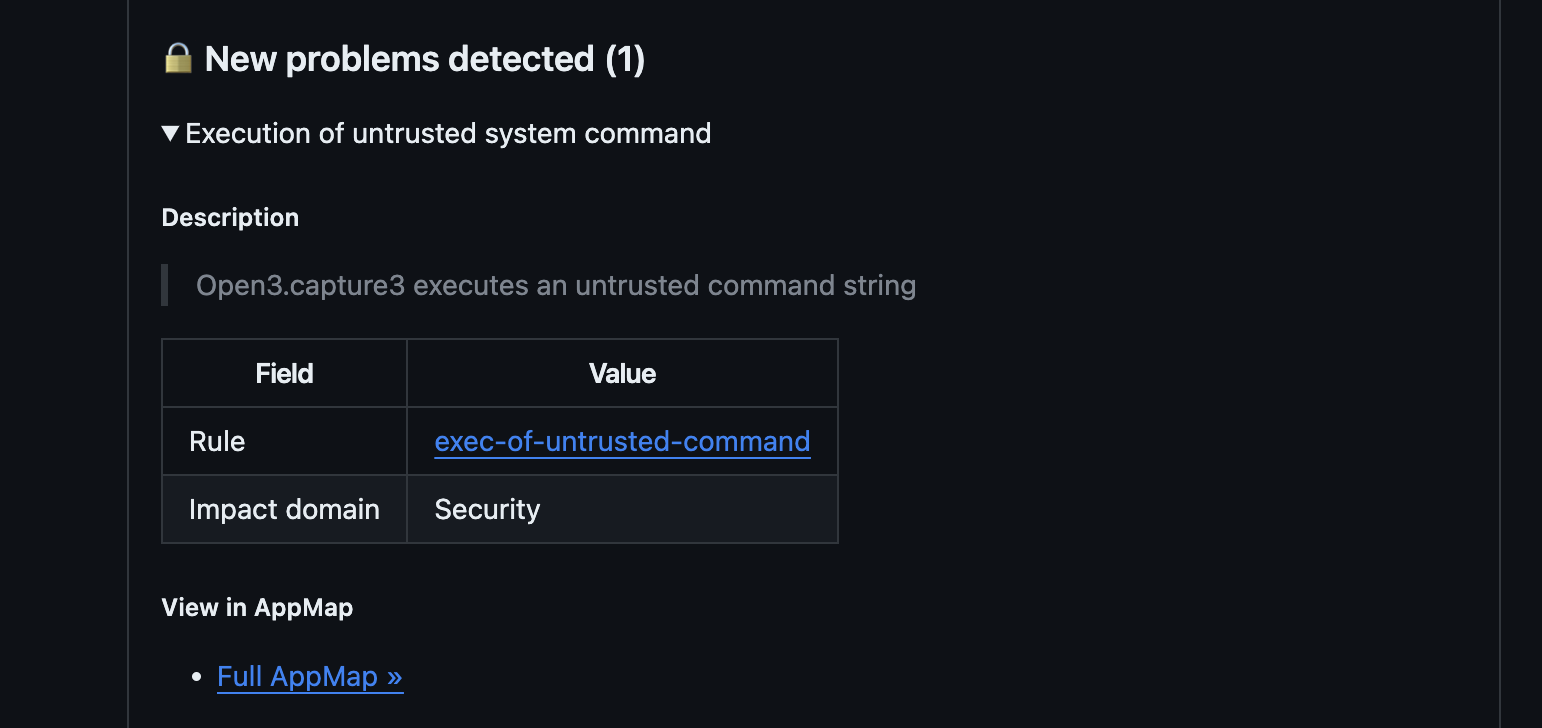
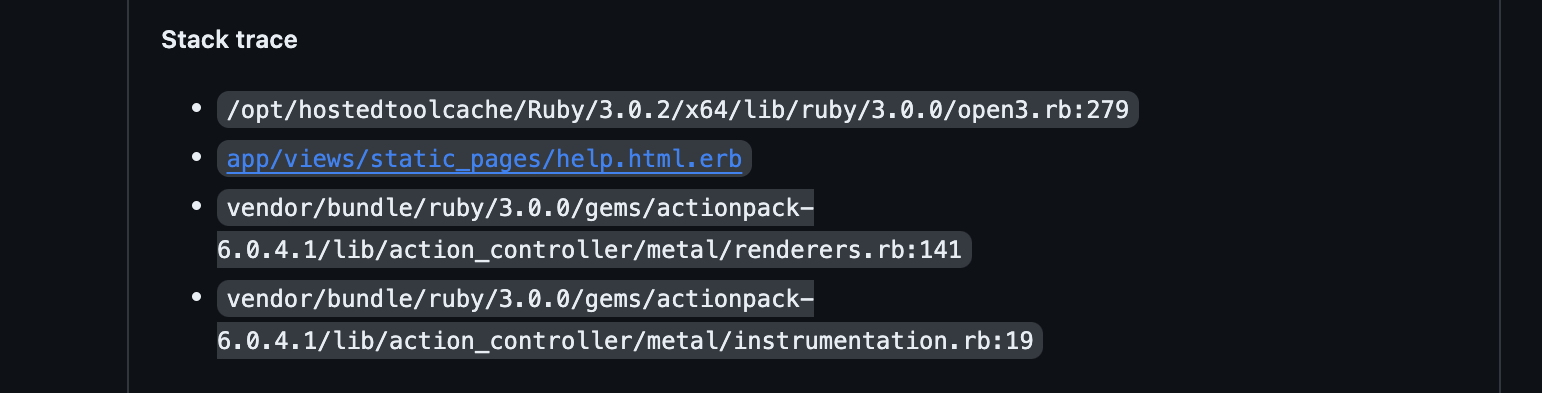
Included in the comment is a stacktrace showing what led to the security flaw, including links to the source code.
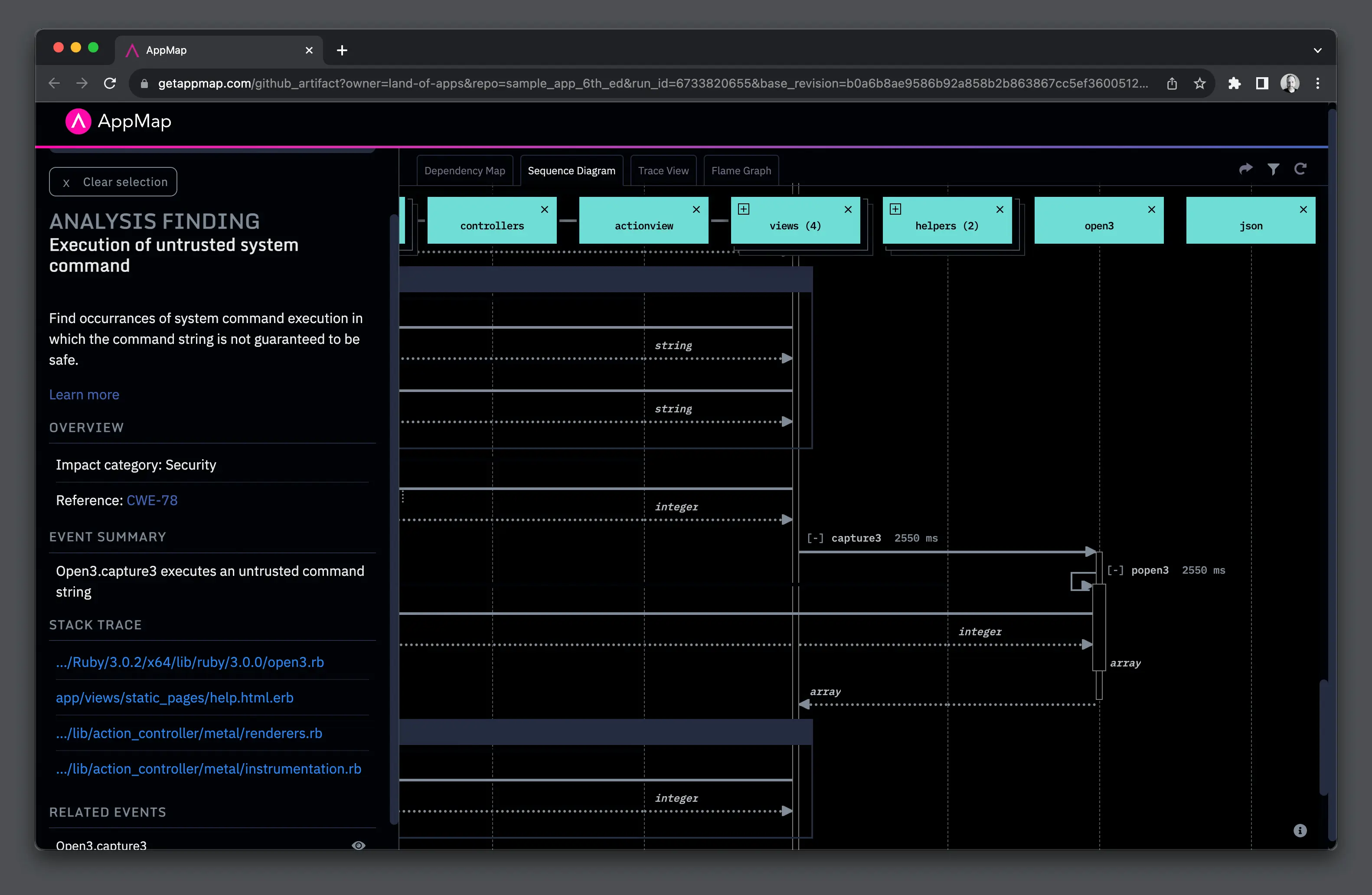
AppMap also provides a full set of interactive visualizations that describe the code behavior that resulted in the security flaw.
To get started, install the AppMap GitHub App from the GitHub Marketplace.
Not ready to try it for yourself? We have example projects on our GitHub so you can check out AppMap for GitHub Actions at work.